The trading world has changed. It used to be a competition among quants; now it’s a race in technology. In 2026, an AI bot is not only ‘rules on/off’ it connects signals with risk filters and execution logic, so trades are placed in a controlled way.
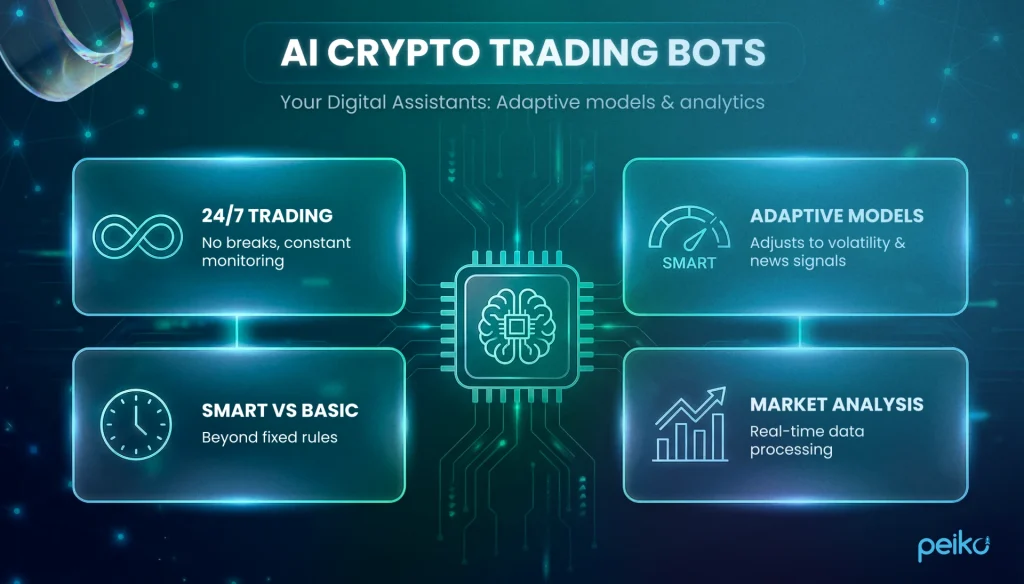
What’s the main difference between old and new AI crypto trading bots? Old bots work like a train on tracks: when there’s a signal, they trade; when there isn’t, they don’t. They don’t account for market panic or regime shifts. A stronger bot can pause entries when volatility jumps, spreads widen, or liquidity drops, so you don’t trade into bad conditions. For a trader, this means fewer avoidable losses and more control.
Why Use AI Crypto Trading Bots?
Crypto bots became popular not just because crypto trades 24/7, but because edge increasingly depends on execution quality and risk overlays. Automation lets you standardize order routing, maker/taker logic, position sizing, and circuit breakers across dozens of pairs and venues-something that breaks down fast in manual workflows.
Thanks to the development of cloud services and stable APIs, it is now possible to set up professional automation without writing complex code from scratch.
Typically, bots are used in the following cases:
- Signal traders: Automate entry into a position based on notifications from TradingView, adding clear loss limits to them.
- System players: Use bots to hedge and rebalance the portfolio, controlling the quality of order execution.
- Arbitrators: Make money on the difference in exchange rates and funding rates between platforms, where every millisecond is important.
Asset managers: Teams that manage multiple accounts on exchanges like Binance or OKX use bots for unified control and reporting.
Why Advanced Traders Use Trading Bots in 2026
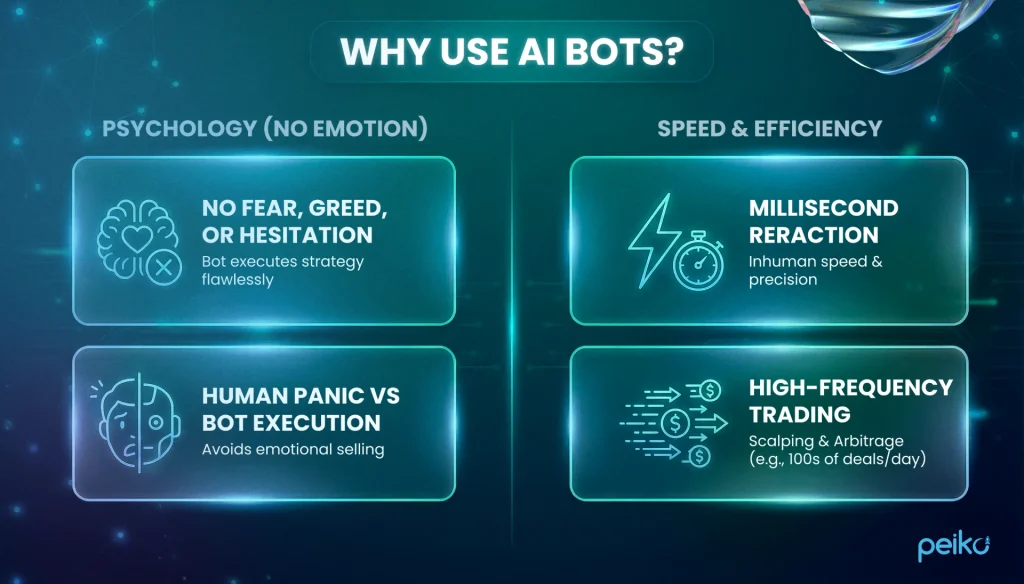
Pros use bots not because they’re lazy, but to stay disciplined. Your biggest enemies are fear and greed. A top AI crypto trading bot has no emotions. It doesn’t panic when the price drops, and it doesn’t chase the top just because everyone else is doing it. It just follows the plan.
The second reason is speed. Humans are slow compared with machines. You can’t look at 50 charts at the same time and instantly calculate spreads. The bot does it in a split second. It can split a large order into smaller chunks to reduce market impact, or capture small price discrepancies (arbitrage) while you’re just opening the crypto exchange app.
Using other people’s bots is good, but creating your own trading platform is a different level altogether. If you are considering starting your own business, we offer professional development for crypto exchanges. We create fast, secure, and convenient turnkey platforms that can withstand heavy loads and compete with the market leaders.
From Strategy to Automation (Advanced Workflow)
How does it work in practice? Think of it as a pipeline, with the bot as the main engine:
- Signal Layer: Where does the buy/sell signal come from? It can be a notification from TradingView, your own code or order-flow analysis. The main thing is that the signal comes with minimal latency.
- Security Filters: This is your safety circuit breaker. The bot checks market conditions. If there is a storm (important news comes out, the price jumps), a smart bot won’t enter the trade to protect your capital.
- Risk Control: How much to buy? The bot itself calculates the position size so that even a series of losses does not wipe out your account / balance. It keeps leverage in check.
- Execution: The final step is execution. The bot decides whether to use a market order (fast, but can cost more via slippage) or place a limit order and wait.
Top Benefits of AI Trading Bot Crypto
System traders choose AI crypto trading bot not just for the sake of automation. The main feature is adaptation. A regular bot blindly executes the program, like a train on rails. AI acts like an experienced driver: it sees the road and reacts to potholes.
- Understanding the situation. A simple bot will buy even in a falling market, because that’s what it’s written in its code. This is a direct path to losses. AI understands the difference between a good trend and a dangerous panic. If the market becomes unpredictable, a smart bot will simply wait out the storm, saving your money.
- Flexible settings. The market changes every day. Old bots have rigid parameters that stop working when volatility increases. AI itself tweaks the settings: if prices start to jump sharply, it will automatically reduce the deal size or move the stop loss so that you are not knocked out of the position by a random movement.
Risks and Limitations to Consider
Even the best ai crypto trading bot is not perfect. Artificial intelligence has its own specific weaknesses that you need to be aware of.
Here are three main risks of using AI:
- The problem of overtraining. A bot can simply memorize price history. It is similar to a student who memorized the answers to last year’s exams. On tests in the past, such a bot shows a perfect result. But when you run it in the real market, it loses money, because the old answers no longer fit the new market questions.
- Finding non-existent relationships. Artificial intelligence sometimes sees patterns where there are none. A bot can suddenly open a strange deal for a large amount simply because of market noise. The worst thing is that you often will not be able to understand the reason for this decision. Unlike simple programs, the internal logic of AI is hidden from the user.
- Helplessness in the face of the new. Models are often lost in non-standard events. If a bot has only learned to trade in a growing market, it may break down during the first crisis. It simply does not have the experience to act in such conditions and may make mistakes where an ordinary person would simply wait on the sidelines.
Types of Crypto Trading Bots
To choose a tool, you need to understand the types of bots. Each of them has its own task and infrastructure requirements.
Arbitrage Bots
- Core idea: Earning on the difference in asset prices on different exchanges or pairs.
- Where it works: Markets where liquidity is unevenly distributed.
- Infra requirements: Requires maximum speed (low latency) and large capital for commissions.
- Failure modes: Delays in withdrawing funds from the exchange, slippage.
Trend-following Bots
- Core idea: Entering a position according to the price movement (Momentum) on breakouts or indicators.
- Where it works: Strong trend movements (bullish or bearish market).
- Infra requirements: Speed requirements are moderate, the main thing is the quality of the signal.
- Failure modes: Lose on “sawdust” (lateral movement), when they often enter and exit with a loss.
Grid Bots
- Core idea: A grid of buy and sell orders within a certain range. We buy cheaper, sell more expensive.
- Where it works: Ideal for flat (sideways) when the price is in a channel.
- Infra requirements: Stable API for constant updating of the grid.
- Failure modes: The price leaves the range – the bot remains with the asset that is falling in price.
Scalping Bots
- Core idea: Many small trades with small profits over short distances.
- Where it works: Highly liquid pairs with low spreads.
- Infra requirements: Fast execution and low trading commissions.
- Failure modes: Technical lags and widening spreads eat up profits.
Copy-trading Bots
- Core idea: Automatic copying of other traders’ trades.
- Where it works: Social trading platforms.
- Infra requirements: Minimum delay between the master’s deal and yours.
- Failure modes: The master changes the strategy or there is not enough liquidity for all subscribers.
Signal Bots
- Core idea: Execution of orders by external commands (TradingView, Telegram).
- Where it works: Universal, it all depends on the quality of the source.
- Infra requirements: Fast processing of webhooks.
- Failure modes: The signal came late or was false.
Sniping Bots
- Core idea: Instant market entry during events like new listings or pool launches to capture primary liquidity.
- Where it works: Short-term windows of opportunity during important events with predictable order flow.
- Infra requirements: Critically low signal latency, strict anti-fraud and fake liquidity filters along with conservative position sizing.
- Failure modes: Significant slippage of the execution price, risk of rapid trend reversal, and increased risk of smart contract vulnerabilities in the network.
AI / ML Trading Bots
- Core idea: Machine learning predicts the price or determines the state of the market.
- Where it works: Complex, non-linear market conditions.
- Infra requirements: Powerful servers for data processing.
- Failure modes: “Black box” (it is not clear why the bot decided so) and retraining the model.
MEV Bots (Maximal Extractable Value)
- Core idea: Reordering transactions in the blockchain to get a profit.
- Where it works: DEX (Uniswap and others).
- Infra requirements: Direct connection to nodes, extreme speed.
- Failure modes: High competition and code complexity.
Sandwich Bots
- Core idea: MEV type: bot buys before a large user transaction and sells immediately after it.
- Where it works: DEX with low liquidity.
- Infra requirements: Real-time mempool monitoring.
- Failure modes: Complex algorithms and protection against such bots (Flashbots).
DeFi Arbitrage Bots
- Core idea: Arbitrage between different DEX protocols.
- Where it works: DeFi ecosystem.
- Infra requirements: Working with smart contracts, gas calculation.
- Failure modes: Errors in contracts, high gas price, front-running.
Best AI Crypto Trading Bots in 2026 (Top Picks & Reviews)
We have selected for you tools that have been proven by time.
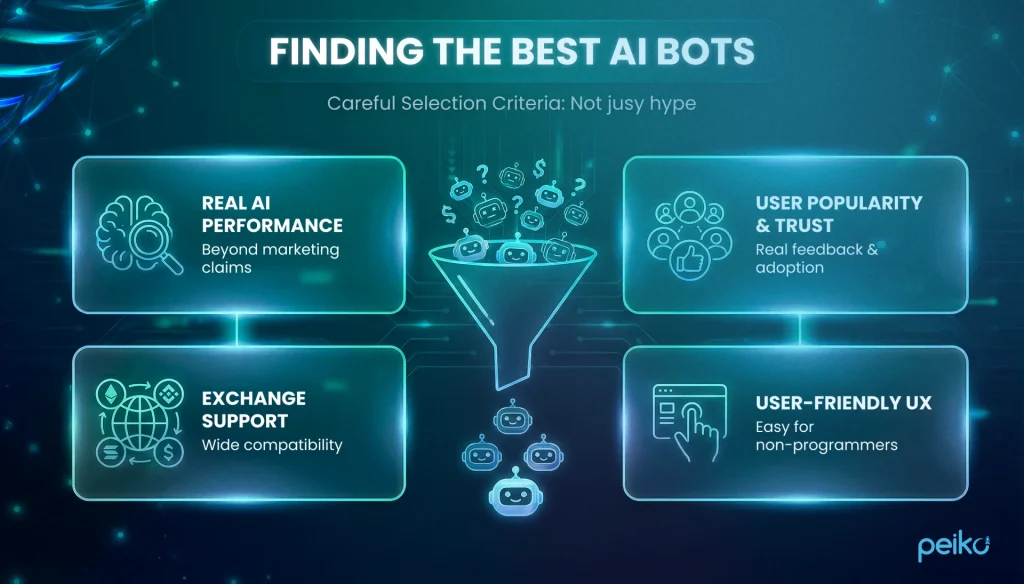
These are platforms where the API does not fall off at the most crucial moment, there are complex types of orders, and which are actually used by professionals for daily work.
3Commas: AI Crypto Trading Bot Overview
3Commas is already a classic for a system trader. The platform is famous for its “Smart Trade” terminal, which allows you to enter a deal manually, but leave the exit (takes and stops) to automation. This is a cloud service that is ideal if you need to manage a bunch of exchange accounts from one window and run DCA bots.
Key AI Features
3Commas supports signal-based entries, and the Gordon bot can suggest DCA parameters using trading history and recent performance data-so you start with data-informed settings instead of guessing.
Supported Exchanges
Works with all the giants: Binance, OKX, Bybit, Coinbase Advanced, Kraken, Bitfinex, Gate.io and over 10 others (18+ in total).
Pricing & Fees
Subscription (tiered plans). No profit-sharing; exchange fees apply separately.
Best For
For DCA strategies, convenient management of many exchanges and smart trading via SmartTrade.
Pros and Cons
- Pros: very user-friendly interface, flexible settings for DCA, stable connection to exchanges.
- Cons: a beginner will have to spend time learning all the features; the Pro version is not cheap.
Cryptohopper: AI Crypto Trading Bot Overview
Cryptohopper is a cloud-hosted bot that can run 24/7. Its feature is a visual strategy builder.e bot running.
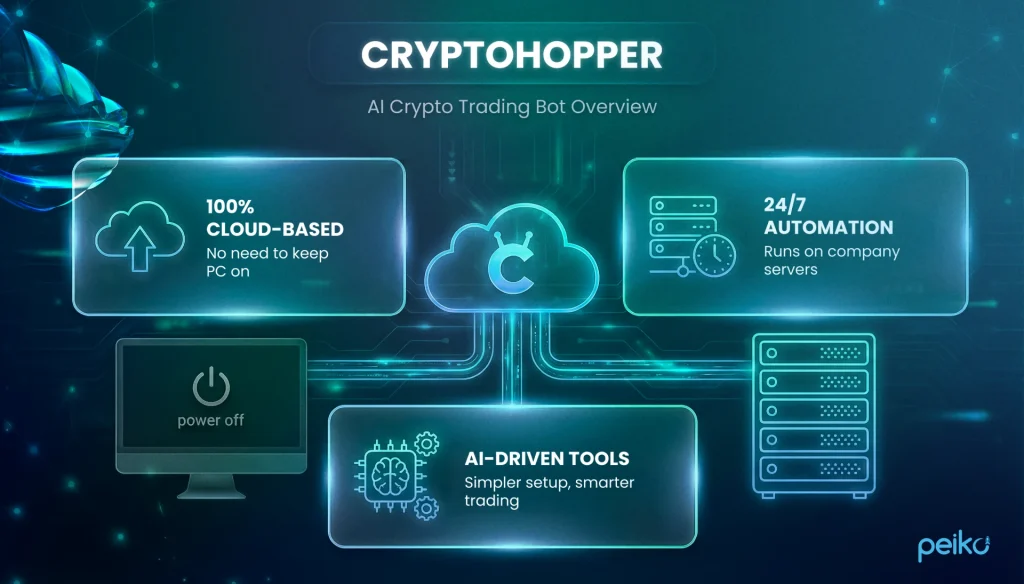
You simply drag and drop blocks (indicators, conditions) via a drag-and-drop strategy builder, and create your bot without code. Well-suited to trend-following workflows.
Key AI Features
Its AI Strategy Designer is a notable feature. It backtests strategies, compares them, and in real time can switch to the strategy most aligned with current market conditions.
Supported Exchanges
Supports major exchanges: Binance, Kraken, Coinbase Advanced, KuCoin, Poloniex (15+ in total).
Pricing & Fees
Subscription (tiered plans, often with a trial/entry tier). No profit-sharing; exchange fees apply separately.
Best For
For those who want to build strategies visually, trade on signals, and do market making.
Pros and Cons
- Pros: runs on the cloud (you can turn off your computer), has a store of ready-made strategies, powerful backtesting.
- Cons: The interface can feel dense for new users; full AI functionality is limited to the top-tier plan.
Pionex: AI Crypto Trading Bot Overview
Pionex is an outlier in this list. It is not a third-party service, but an exchange with built-in trading bots.
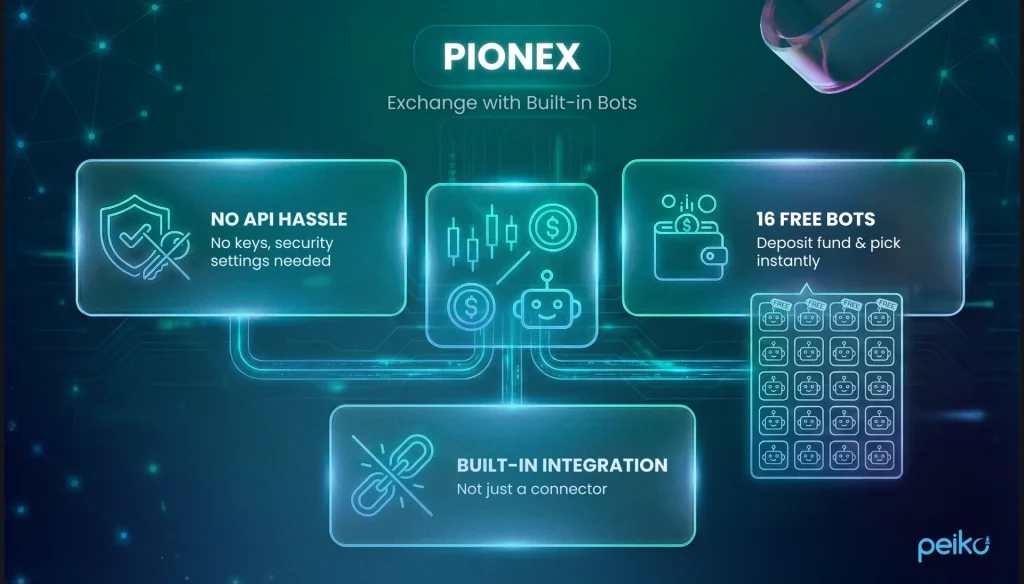
Thanks to this, it reduces API-latency and connectivity issues typical of third-party tools. They take liquidity from top exchanges, which can improve order execution consistency.
Key AI Features
The AI assistant is very helpful with Grid bots. Instead of manually selecting grid boundaries, artificial intelligence analyzes recent historical volatility and suggests grid parameters.
Supported Exchanges
Pionex is the exchange itself (built-in bots), so trades run directly on Pionex rather than via API connections to external exchanges.
Pricing & Fees
Free (fees only). Bots are included; you pay standard exchange trading fees. No subscription and no profit-sharing.
Best For
For high-frequency Grid trading and those who want to save on commissions.
Pros and Cons
- Pros: low commissions, built-in liquidity, 16 free bots.
- Cons: Requires keeping funds on-exchange (custodial risk), you can’t connect your other exchanges.
Bitsgap: AI Crypto Trading Bot Overview
Bitsgap is a top choice for Grid tradinraders struggle to find opportunities in a flat market.
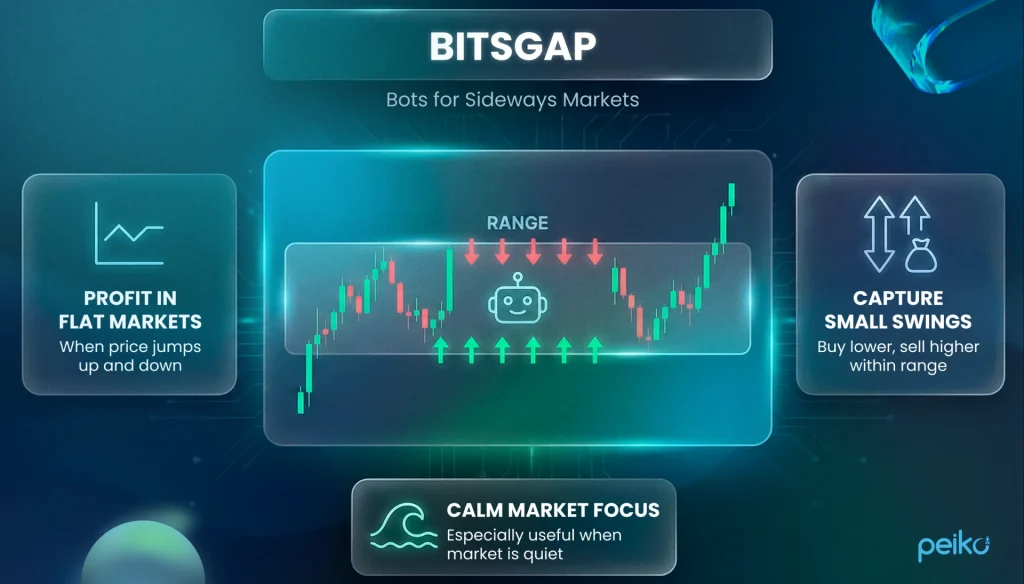
It has a single terminal to connect to a wide range of exchanges, making it a centralized terminal for arbitrage and grid strategies.
Key AI Features
Smart order routing, volatility/pump filters, and a trailing feature that can shift the grid as price moves to reduce premature exits.
Supported Exchanges
Huge list: Binance, OKX, Bybit, KuCoin and 25+ more.
Pricing & Fees
Subscription (tiered plans). No profit-sharing; exchange fees apply separately.
Best For
For Grid trading, range scalping, and cross-exchange arbitrage.
Pros and Cons
- Pros: probably the best visualization of the grid on the chart, there is a demo mode, generally reliable in day-to-day use.
- Cons: No dedicated mobile app (web-only), for an unlimited number of bots you need an expensive plan.
TradeSanta: AI Crypto Trading Bot Overview
TradeSanta is positioned as a streamlined automation tool. This is a cloud service that focuses on DCA and Grid bots. It supports both long and short configurations, including futures (where supported by the exchange).
Key AI Features
Uses signals from popular indicators (MACD, RSI) to identify potential entry points. There are also risk filters to avoid entries under elevated risk conditions (e.g., extreme volatility).
Supported Exchanges
Main players: Binance, Huobi, OKX, Coinbase Advanced, Bybit (8+ in total).
Pricing & Fees
Subscription (tiered plans). No profit-sharing; exchange fees apply separately.
Best For
For simple automation and futures trading without unnecessary complications.
Pros and Cons
- Pros: low price, futures support, intuitive dashboard.
- Cons: May lack granular controls for advanced users.
Coinrule: AI Crypto Trading Bot Overview
Coinrule is built around IF-THEN rule logic. It’s a rule builder that allows you to build strategies from logical blocks.
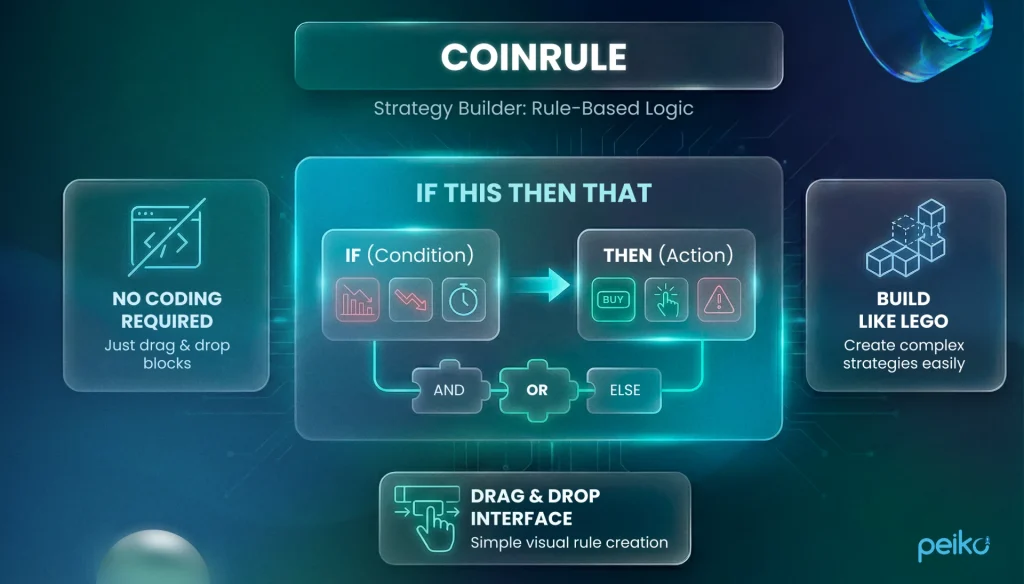
Ideal for those who want to create rules for portfolio risk management without coding.
Key AI Features
Supports pattern-based conditions and historical testing. The main feature is conditional logic that can connect different coins. For example: “If Bitcoin drops 5%, sell ETH into USD (or a USD stablecoin)”.
Supported Exchanges
Binance, Coinbase, Kraken, Bitstamp (10+ in total).
Pricing & Fees
Free + Subscription tiers. No profit-sharing; exchange fees apply separately.
Best For
For creating logical chains, portfolio rebalancing, and hedging.
Pros and Cons
- Pros: Very intuitive rule builder, clean design, lots of training materials.
- Cons: Execution latency may be higher than direct exchange-native scripts; can be costly at the professional tier.
WunderTrading: AI Crypto Trading Bot Overview
WunderTrading is a bridge between TradingView and a live exchange. If you build strategies in TradingView (Pine Script), this service can execute them on an exchange via webhooks. There’s also a strong copy trading platform.
Key AI Features
AI-based ranking helps surface traders for copy trading. There’s also spread analysis to find arbitrage opportunities.
Supported Exchanges
Binance, Bybit, Deribit, BitMEX, OKX (15+ in total).
Pricing & Fees
Free + Subscription tiers. Copy-trading may also involve performance/profit-sharing fees set by the trader you follow; exchange fees apply separately.
Best For
For automating strategies with TradingView, copy trading, and derivatives trading.
Pros and Cons
- Pros: works perfectly with webhooks, supports spread terminal, low price.
- Cons: Works best if you’re comfortable with TradingView workflows.
Comparison Table – Best AI Crypto Trading Bots
| Bot name | AI level (Basic/Advanced) | Supported exchanges (examples) | Pricing (type) | Best for | Primary use / type |
| 3Commas | Advanced | Binance, OKX, Bybit, Coinbase, Kraken | Subscription | Multi-exchange execution, DCA, SmartTrade | DCA, execution tooling |
| Cryptohopper | Advanced | Binance, Kraken, Coinbase, KuCoin | Subscription | Visual strategy building, signals, backtesting | Trend, signal-based |
| Pionex | Basic | Pionex (built-in) | Free (fees only) | Low-friction grid/rebalancing | Grid, rebalancing |
| Bitsgap | Advanced | Binance, OKX, Bybit, KuCoin | Subscription | Grid/range trading, arbitrage workflows | Grid, arbitrage |
| TradeSanta | Basic | Binance, OKX, Bybit, Coinbase | Subscription | Simple DCA/Grid automation | DCA, grid |
| Coinrule | Basic/Intermediate | Binance, Coinbase, Kraken, Bitstamp | Free + Subscription | Rule-based portfolio logic, hedging | IFTTT, hedging |
| WunderTrading | Intermediate | Binance, Bybit, OKX, Deribit | Free + Subscription (+ possible profit-sharing via copy trading) | TradingView webhooks, copy trading | Signals, copy-trading |
How to Choose an AI Crypto Trading Bot?
Choosing a bot is like choosing a reliable business partner. If you pick the first one you see, you risk wasting time and money.

To avoid mistakes, here’s a simple checklist to help you choose:
- Security and access. This is the base. Use trade-only API keys, turn on IP restrictions if possible, rotate keys, and store them safely, treat it like production access. Be sure to set up two-factor authentication and restrict access by IP address so that no one else can use your account.
- Reliability check. Don’t believe advertising, believe uptime. Check reliability in a practical way: incident history/status updates, what happens after disconnects, and how they handle partial fills and stuck orders. It is important to understand how the bot behaves when the exchange makes errors. Stability of work is more important than a beautiful interface.
- Execution tools. The bot should be able to save your money. Look for Post-Only functions for a guaranteed maker discount and Reduce-Only so as not to accidentally open an unnecessary position. This is critical for systematic trading.
- Risk management. The bot should have brakes. A Kill-switch function is necessary to stop trading when the daily loss limit is reached. This is your last line of defense.
- Strategy suitability. Choose a tool for a specific task. Grid trading requires 24/7 stability. Speed is critical for arbitrage. Clear stop-losses are important for trend strategies.
- Economic model. Calculate the full cost of the business. The subscription price is just the tip of the iceberg. The main costs are trading commissions and price slippage. If the bot is slow or inaccurate, you will lose more in commissions than the most expensive software costs.
Off-the-shelf bots have limits because they are built for the masses. If your strategy requires unique logic or you want to build your own platform, you need a custom solution.

Let's build something great together